In the previous article, we describe tutorial on configuring Browser Capabilities Protection. In this article, we will describe how to configure Action Log in Magento 2 admin panel.
The Action Log allows store administrators to track activities of other administrators in your stores. For most events, the action, the user who performed action, the result of the action, and the ID of the object on which the action was performed are included in the available information. Action Log is very important for your Magento 2 online store because you can track activities of administrators effectively and manage their actions. Furthermore, you can detect if hackers are hijacking right to control your website or not, and remove them out of your admin roles as fast as you can. So you have to configure action log and tracking every single action of other store administrators carefully.
To configure the Action Log, you have to follow these steps:
On the admin sidebar, click Stores. Under Settings, click Configuration.
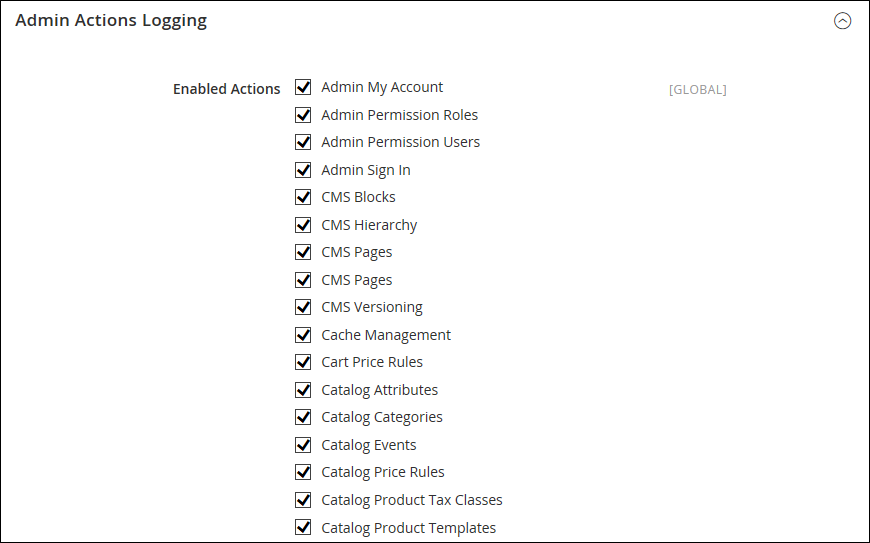
On the left of the panel under Advanced, click Admin.
Open the Admin Actions Logging, select and mark any checkbox to enable actions logging as you want. There are 17 actions logs to choose in the global scope, so you have to choose wisely and do not miss anything.
Click Save Config after completed.
Above is a tutorial on how to configure action log in Magento 2 admin panel. We hope that you will know how to select action logs, oversee the action of other administrators carefully, manage other store administrators under your command and run your online store smoothly. If you have any question or have any edit request, feel free to leave a comment or contact us directly. In the next article, we will describe tools and cache management in Magento 2. See you in the next blog post.